 In the context of mobile security, physical attacks involve any technique that gains unauthorized access to a device by touching it or physically interacting with it. Physical attacks usually have a relatively low barrier to entry, meaning unskilled attackers without security or programming knowledge can do it. Despite its rampant prevalence, physical attacks are still ignored by many experts in digital security. In this blog post I will be focusing on techniques for hacking smartphones, but these attacks will work against any electronic device. Because of their practicality we’ve prioritized Armadillo Phone to resist physical attacks that other phones are extremely vulnerable to. Ultimately, physical attacks are one of the most potent and simplest ways to hack anything… as long as you can get your hands on it.
In the context of mobile security, physical attacks involve any technique that gains unauthorized access to a device by touching it or physically interacting with it. Physical attacks usually have a relatively low barrier to entry, meaning unskilled attackers without security or programming knowledge can do it. Despite its rampant prevalence, physical attacks are still ignored by many experts in digital security. In this blog post I will be focusing on techniques for hacking smartphones, but these attacks will work against any electronic device. Because of their practicality we’ve prioritized Armadillo Phone to resist physical attacks that other phones are extremely vulnerable to. Ultimately, physical attacks are one of the most potent and simplest ways to hack anything… as long as you can get your hands on it.
Getting physical (access)
 NSA agents intercepting Cisco routers for malicious tampering
NSA agents intercepting Cisco routers for malicious tampering
Usually the hardest part of performing physical attacks is getting access to a target. Different devices have varying levels of opportunity for attack, for example a public kiosk or ATM is designed to be used by anonymous public users. While smartphones offer a great opportunity for physical attacks (because they’re easier to steal or get access to), they also have lockscreens and theft protection. Physical attacks against smartphones are sometimes harder to perform because they can’t be easily disassembled like desktop computers. Desktop computers and servers are more physically protected, being inside of locked buildings, which increases the risk for attackers. Datacenters use biometric sensors and double-doored “air-locked” entrances to deter intruders. Despite all the nuances, for the most part the physical threat level between most devices is roughly equivalent. It’s important to realize that devices can be tampered with at any layer of the supply chain, not just once it’s in the user’s hands. Many more people have physical access to a device over its lifetime than its owners typically realize. Vendors, manufacturers, component makers, delivery people and even repair techs are all capable of accessing your hardware. Physical access is especially easy for state-sponsored attackers, because they can simply intercept any packages passing through their countries, or seize someone’s property if they’re a domestic target.
 When attempting to gain physical access to a target, surveillance and intelligence are the most important tools an attacker can use. Knowing the routine and behaviour of a target dramatically increases your ability to perform attacks, and make sure you remain undetected. For example, if you know when a person leaves for work every day it will be much easier to tamper with their home PC. Because people increasingly own multiple devices (PC, laptop, smartphone) for different situations it’s common for them to leave at least one of them unattended.
When attempting to gain physical access to a target, surveillance and intelligence are the most important tools an attacker can use. Knowing the routine and behaviour of a target dramatically increases your ability to perform attacks, and make sure you remain undetected. For example, if you know when a person leaves for work every day it will be much easier to tamper with their home PC. Because people increasingly own multiple devices (PC, laptop, smartphone) for different situations it’s common for them to leave at least one of them unattended.
The way a hacker approaches a target is often the most crucial aspect to determine how suspicious an attack will be to a victim. Getting a victim to connect their device to something you’ve already hacked (a “watering hole” attack) is an effective way to lure targets without raising suspicion. Another method could be replacing their device with one designed to record their passwords ( an “evil maid” attack ).
If the victim never knows you even interacted with them, they’re unlikely to ever realize they’ve been hacked. One level below that would be an interaction where they notice you, but don’t realize you’ve physically accessed their devices. Conversely, if you have to use a flimsy pretext to get access to their devices and they’re aware of it they may become extremely paranoid. Also remember: if all else fails, you can always ditch elegant access methods and just steal their stuff. Hitting someone in the head and running off with their phone is a surprisingly common attack vector.
Example: NSA package interdiction
- Intercepting packages while they're being delivered is one of the stealthier ways of gaining physical access.
- Shipping can take unexpected routes without causing too much suspicion and parcels need to wait for customs inspection anyways.
- Packages can be intercepted in the country they originate in and any country along the way to the recipient.
- A file from the 2014 Snowden leaks clearly details an example of the NSA intercepting packages leaving the United States.
- Care was taken not to damage the packaging to avoid suspicion. Tape was removed by using a hair driver to heat up the adhesive and slowly peeling it off so it wouldn't leave any marks.
- Although it's easier for state-sponsored attackers, anyone who monitors the recipient can intercept packages by replacing them before they notice.
- Shipping companies can also intercept packages they handle, as well as any of their rogue employees.

Example: Ross Ulbricht's laptop
- Ross Ulbricht is a man currently serving a life sentence for creating the "Silkroad" darknet drug market.
- FBI agents were nearing the end of their investigation on Ulbricht and were doing close surveillance on him prior to his arrest.
- He was known to carry an encrypted laptop they believed was used to manage Silkroad. This laptop was heavily protected and would re-encrypt itself when not in use or if it became inactive.
- On the day of his arrest the FBI followed him to a public library where he was using this laptop to manage Silkroad.
- A male and female agent started a loud argument near him in order to distract Ulbricht.
- When Ulbricht turned around to look at the angry 'couple', the man pushed the unlocked laptop across the table to the woman who handed it to another FBI agent. The agents intermittently pressed a key while photographing data on the laptop to keep it from automatically locking.
- By using a simple physical attack they were able to bypass all his software protection. After FBI agents arrested Ulbricht they used evidence obtained from the laptop to convict him of many crimes.

Example: Autorun USB drives
- A common attack that worked against Windows before it was effectively killed by Microsoft
- The attack revolved around the ability to create USB drives that automatically launched programs stored on the drives when they were connected to a Windows computer.
- This led to an easy attack vector: leave malicious USB drives near the target you want to hack, then hope they pick them up and plug them into a PC running Windows
- In practice this is surprisingly effective as people are curious by nature, despite any training they have.

Gentle touch
A ‘gentle’ physical attack is one that can be performed quickly and easily without permanently modifying the hardware. This means you can hack things without disassembling them, leaving any damage or anyone even noticing it’s been hacked. Normal user input performed by a human that results in a device being hacked would be one of the simplest examples. In some cases, (like ‘smudge attacks’ that look for marks on a user’s smartphone to indicate their unlock pattern) an attack may be so gentle that you don’t even need to physically touch the device. Other attacks use sound or RFID to interact with nearby devices without touching them. However, in most cases gentle attacks are the result of abusing a designated interface that is meant to connect to an external device. Malicious peripherals (evil keyboards, mice, USB drives) are a technique like this that can compromise both PCs and smartphones. People often connect peripherals to different computers, this means it can potentially compromise multiple devices if the attacker’s lucky.
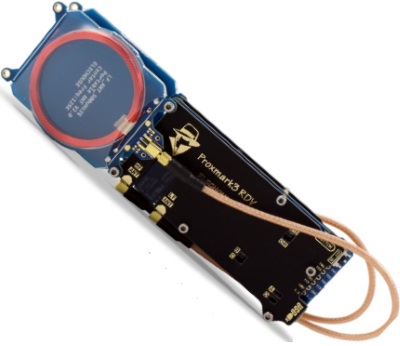
Example: Hacking smartphones with NFC
- Near Field Communications (NFC) is a technology used to transfer data by reading data tags, typically within 1 inch of a device.
- NFC is used in many smartphones as well as credit and debit cards.
- Multiple exploits have been found in both Android and iOS that allow a malicious NFC tag to exploit the phone.
- To trigger the exploits an attacker only needs to get close to the victim and tap something against their phone.
- Similar attack vectors (physically tapping against victim's pockets) have also been used to steal NFC credit card information.
- Directional NFC antennas can also be specifically crafted to increase the range on NFC scanning and potentially deliver the attacks slightly further than 1 inch.
Example: Breaking PGP with sound
- By measuring electrical emissions of an electronic device it's possible to figure out what instructions are being performed inside the device.
- Although it can be difficult or error-prone if there is too much noise, under good conditions this can be an effective way to extract data from a machine.
- RSA is the underlying algorithm behind PGP. Because RSA must follow an easily recognizable pattern to generate or decrypt encryption keys, it's possible for an attacker to extract encryption keys.
- Using sound, researchers can deduce the electrical activity on the device, then use that to extract the encryption key the device is using.
- Although the sound attack mentioned has only been tested against laptops, it could be easily applied to smartphones.
- While technically this isn't a purely "physical attack" it still requires physical proximity to do.

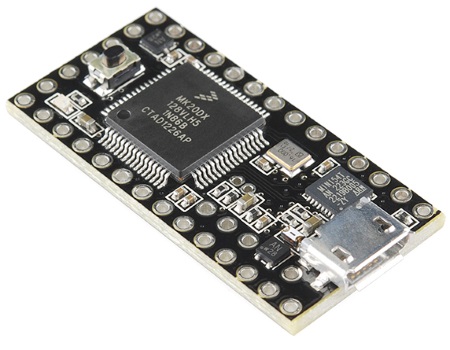
Example: iCloud theft protection bypass
- In 2013 I released a program called iCloudHacker that bypassed Apple's theft protection for Macbooks.
- The theft protection for iCloud involved user's setting a custom 4-digit recovery password after declaring it stolen.
- The program ran on a Teensy microcontroller and connected to the Macbook over USB, pretending to be a mouse and keyboard.
- The program guessed all possible recovery passwords one at a time (from 0000-9999) by sending the Macbook fake mouse and keyboard input that mimicked a normal person typing in a password and hitting enter.
- Apple had delays for guessing passwords by timing out for 30s and then 5 minutes if the user made too many failed attempts.
- The delays were bypassed by using the fake mouse to click the restart button and restart the Macbook, then continue guessing.
- Using these techniques it could hack any stolen MacBook within 48 hours.
Example: Shoulder surfing
- Shoulder surfing is the act of looking at an oblivious victim's screen (usually while behind them) to steal their password.
- This is one of the oldest and most effective hacking techniques in existence, especially against smartphones.
- Shoulder surfing works best against people who are intoxicated or bad typers because they will have to type their password multiple times, giving an attacker more chances to see what it is.
- This doesn't have to involve being physically near them, attacks have been performed by using video camera surveillance.
- Algorithms have even been developed to automatically shoulder surf with camera footage from in front of a victim by guessing with machine learning where their fingers likely were.

Rough touch
A ‘rough’ physical attack is one that’s performed by permanently modifying a target device. This can mean disassembling and replacing internal components so the victim remains unaware, however it can also include complete destruction of the device. Rough attacks should be considered as a last result, when gentle attacks aren’t proving effective or if an attacker doesn’t care if the victim finds out they’re being targeted.
Rough attacks will usually target the circuit board components themselves rather than interfacing through any designated interface like a gentle attack. These types of attacks can involve replacing components, modifying components, or interfering with the device. Electrical attacks can be performed against components by changing the amount of electrical current they’re receiving to cause glitches and other unexpected behaviour.
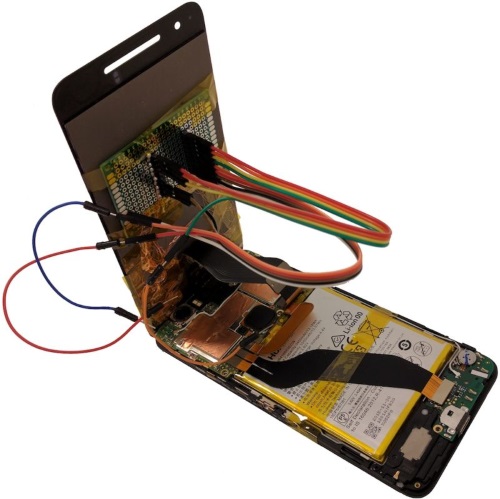
Example: malicious touchscreens
- Recently researchers from Ben-Gurion University of the Negev have shown how to use malicious touchscreens to hack smartphones.
- These touchscreens can steal passwords, install applications and generally do whatever a normal user could
- The malicious replacements use chips intercept data between the phone and the screen to perform attacks.
- Although these were only installed in the Nexus 6P and LG G Pad 7.0, these attacks could potentially apply to any smartphone.
- More than half of people who own a smartphone have damaged their screen at least once, so the idea of a malicious replacement screen seems very viable.
- Component tampering like this is extremely difficult to detect unless the phone is disassembled and inspected.
- Malicious components including motherboards, NICs and graphics cards have been a well-researched threat.
Example: cold-boot attacks
- Normally the RAM in your phone or computer (which stores your passwords & application data) becomes corrupted as soon as it's powered off.
- However, under extremely cold temperatures the RAM can persist for several seconds or minutes after it's lost electrical current.
- Attackers can use this to exploit devices that are decrypted but locked and retrieve the victim's password.
- This attack is particularly effective against PCs but can be used on smartphones as well.
- By lowering the temperature to -20C a phone's RAM can be persist for several seconds to minutes.
- Once the temperature is lowered an attacker can quickly flash new firmware that immediately searches the memory for a user's password.
- Cold-boot attacks like this can be used to bypass storage encryption or retrieve sensitive information.

-
Published on: Aug 27th, 2017
