 Encryption is making data unreadable to an attacker. Deniable encryption is encrypting data in a way that the user can deny the encrypted data even exists. For example, on Armadillo Phone you can have an unlimited amount of fake users with fake data and apps. If an attacker forces a victim to reveal their password, they can give a fake user’s password instead of their real password. Deniable encryption is different than steganography ( hiding data in plain sight, like storing hidden text in an image ), because the data’s confidentiality is guaranteed by encryption.
Encryption is making data unreadable to an attacker. Deniable encryption is encrypting data in a way that the user can deny the encrypted data even exists. For example, on Armadillo Phone you can have an unlimited amount of fake users with fake data and apps. If an attacker forces a victim to reveal their password, they can give a fake user’s password instead of their real password. Deniable encryption is different than steganography ( hiding data in plain sight, like storing hidden text in an image ), because the data’s confidentiality is guaranteed by encryption.
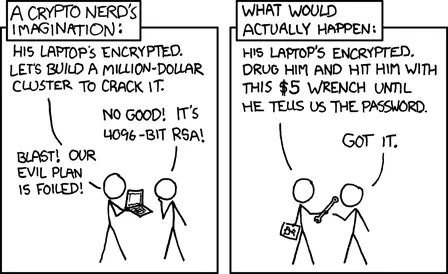
Software developers often forget that in many places violence, torture, corruption and authoritarian governments are an unfortunate reality. Deniable encryption helps defend against these threats by protecting the user’s data, even when the user can’t protect themselves.
We have spent years improving Android’s storage to make it more secure and deniable. Armadillo Phone has the most secure storage encryption of any mobile device we’re aware of. Armadillo Phone’s deniable encryption means your files are better protected against the criminals, corporations and foreign governments trying to spy on you. Here’s how we made those improvements.
Full-Disk Encryption
The most prominent academic projects to explore deniable encryption on Android are MobiFlage and variants such as MobiHydra. These projects are based on Android’s old Full-Disk Encryption ( FDE ) system. Deniable FDE works by storing the data of hidden users in what appears to be unused space. FDE has many drawbacks:
- Users can accidentally overwrite each other, which causes total data loss
- Disk space is wasted by being equally divided among each user
- Limited amount of maximum users
- FDE is no longer supported since Android 9
- Must reboot the phone to switch to another user
The main problem is that these systems are not truly deniable. With FDE, if an attacker is holding your locked phone and asking you to unlock it, you cannot give them the password for a decoy user without first restarting the device. This means an attacker could easily break deniability.
File-Based Encryption
Armadillo Phone 2’s encryption is based on Android’s new File-Based Encryption ( FBE ). The main benefit of FBE over FDE is that we can switch users instantly, which greatly increases deniability. Multiple users can even run in the background at the same time. There are also several other benefits:
- Impossible to overwrite other users
- Diskspace is allocated according to usage
- Unlimited amount of users
- FDE is fully supported with latest versions of Android
- Don’t have to reboot the phone to switch users
Improvements
Although FBE has it’s own set of weaknesses vs FDE, we have made several improvements to mitigate them. Overall, we believe these combined changes make Armadillo’s FBE significantly more secure:
1. Switch users instantly:
With Armadillo Phone 2, you can instantly switch to any other user in real-time by simply entering their password into the lockscreen of any user. This allows you to login to a fake user without an attacker noticing, if you’re forced to reveal your password.
2. Improved metadata encryption:
Android’s first FBE implementation in Android 7 was a significant downgrade for privacy versus FDE. It didn’t encrypt metadata ( such as file size, last modification date, etc. ) like FDE does. Android 9 introduced metadata encryption for FBE, but it only encrypts metadata with a single key for all users. This means that if one user reveals their password, it exposes the metadata for other users on the phone, which hurts deniability.
Armadillo has improved Android’s FBE by encrypting the metadata of each user separately. With Armadillo Phone, revealing one user’s password won’t expose other users metadata.
3. Equal users:
In Android there are two classes of users: the primary user and secondary users. The primary user MUST be unlocked before any secondary user can be unlocked. The primary user is also the only one with access to many important security features, like wiping the device. This primary user breaks deniable encryption: all an attacker has to do is force the user to reboot their phone and enter their password to discover their primary password.
Armadillo Phone doesn’t require a primary user to unlock it before the rest can be unlocked. With Armadillo, secondary users can do anything a primary user can, including logging in after rebooting the phone, setting security policies or wiping the phone.
4. Fake users:
Although the device’s firmware makes reading encrypted data off the disk impossible, there are “chip-off attacks” that remove the device’s storage hardware to read the data directly. This technique is extremely difficult and expensive, so it’s typically reserved for state-sponsored attackers. Although the file contents, names and metadata are all encrypted, an attacker using this attack could still see how many users there are. They could then demand the victim give them passwords for each user they see.
Armadillo Phone mitigates this by creating a random amount of “fake users” filled with random data. This way an attacker cannot easily tell which users are real, even if they recover encrypted data directly off the device. Chip-off attacks are also mitigated by to the Titan M security chip.
5. Hardened KDF
The key derivation function ( KDF ) is the process of turning a password into an encryption key. Android uses Scrypt as the KDF. Scrypt is known to be “memory hard”, which means it requires both CPU and RAM, so dedicated hardware cannot be easily created to crack it. Scrypt uses “work factors” to determine how strongly encrypted each password is.
Armadillo has strengthened Scrypt’s work factors to make it more difficult to crack. The work factors have been increased from 15:3:1 to 19:4:1 , which is an increase in complexity from 32,768 iterations to 524,288 iterations. These work factors were chosen to use the maximum amount of CPU and RAM on the Armadillo Phone 2’s hardware. This hardening slightly increases the time required each time to check if a password matches before unlocking the device. This also makes it exponentially harder for an attacker to attempt to guess the user’s password, because the extra time is added to each guess.
Performance
Because Armadillo Phone is made with privacy as the top priority, we can afford to sacrifice some performance to achieve better security. Our storage encryption improvements do make things slightly slower, but this is a trade our clients are happy to make if it helps better protect their data. Generally, Armadillo’s improvements only occur when first initializing the device, or when unlocking a user after rebooting. Once an Armadillo Phone has been unlocked and is in use, the storage encryption performance is only 1.3% slower than Android. You can read more about Armadillo Phone’s different types of encryption here

-
Published on: Mar 28th, 2021
